OpenClaw 2026 Security Deployment Manual: Building a Zero-Leak AI Agent Fortress
As AI Agents move into enterprise-grade applications, security is no longer an option—it's the baseline for survival. OpenClaw v2026.2.26 brings not just performance improvements, but a new "fortress-level" security architecture. Combined with VPSMAC's physically isolated Mac compute nodes, we'll show you how to implement 11 key hardening steps to build an impenetrable environment.
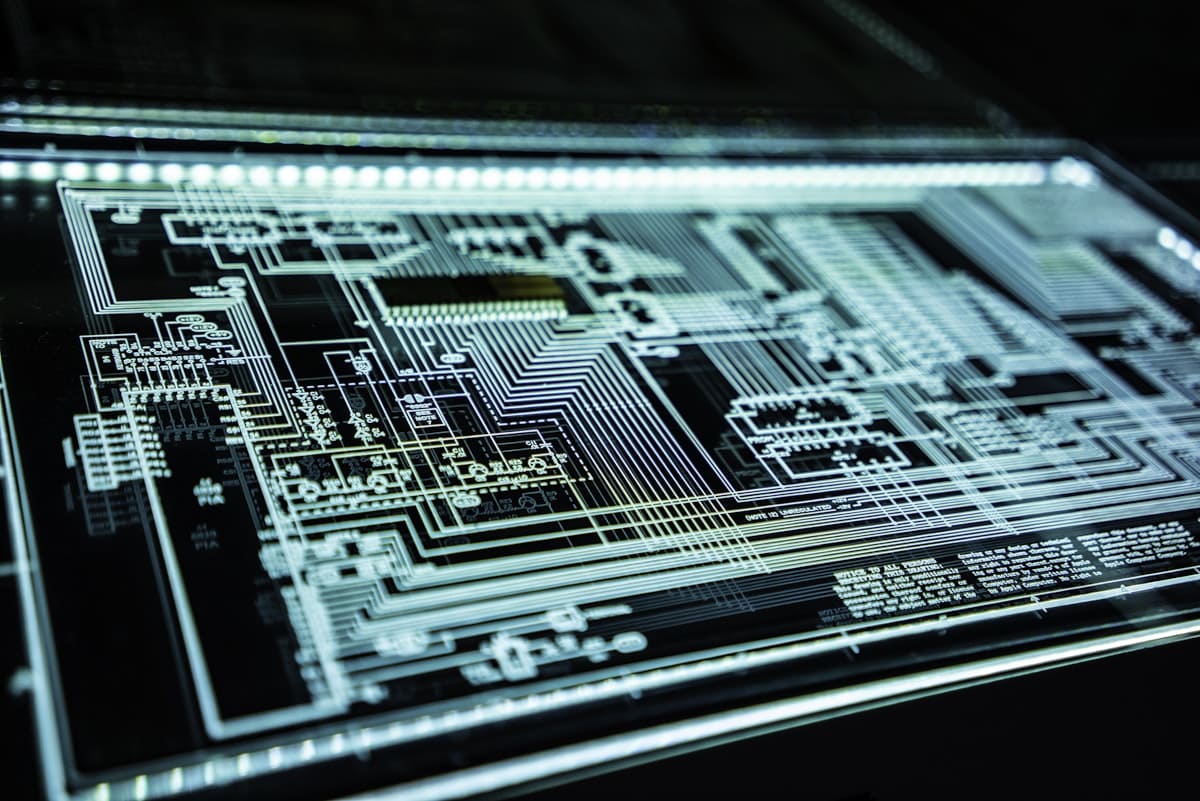
Introduction: Physical Isolation is the Last Line of Defense
Why deploy OpenClaw on a bare-metal Mac from VPSMAC instead of just any virtual machine? The answer lies in physical isolation. Traditional public cloud VMs are vulnerable to "Side-Channel Attacks," where malicious tenants could steal your API keys via shared CPU caches. At VPSMAC, you have independent control over an entire physical M4 chip, cutting off information leaks at the hardware level.
Phase 1: Deep Dive into the New Secrets Auditing in v2026.2.26
The latest version introduces the `openclaw-audit` tool, providing real-time monitoring of key call paths in memory. Even if a third-party library in your code attempts to exfiltrate keys, the audit engine will immediately intercept and trigger an alert.
# Enable live Secrets auditing mode openclaw-audit --enable-live-tracking --severity high # View audit log summary openclaw-audit summary
Phase 2: The 11-Step Security Hardening Checklist
To build a "zero-leak" environment on VPSMAC, ensure you execute these 11 critical hardening operations:
OpenClaw Fortress Hardening Checklist
- Full Disk Encryption: Enable FileVault on macOS to ensure data is unreadable if physical media is compromised.
- SSH Key Hardening: Disable password login; allow only ed25519 hardware security keys.
- Firewall Whitelisting: Use `pfctl` to restrict AI agent traffic only to necessary API domains (e.g., api.openai.com).
- Secrets Isolation: Store keys on an encrypted RAMDisk that is wiped upon shutdown.
- TCC Permission Minimization: Grant OpenClaw only essential Accessibility and Screen Recording permissions.
- SIP Lockdown: Ensure System Integrity Protection (SIP) remains strictly enabled.
- Process Fingerprinting: Enable built-in code signature cross-verification in OpenClaw.
- MFA Enforcement: Require hardware 2FA tokens for all remote management sessions.
- Log Offloading: Stream security logs in real-time through encrypted tunnels to an independent audit node.
- Auto-Patching: Configure automatic updates to keep T2/M4 firmware always current.
- Sandboxed Execution: Run untrusted custom AI scripts using `sandbox-exec`.
Phase 3: Hands-on —— Building an Encrypted RAMDisk for Secrets
We'll demonstrate how to use a macOS RAMDisk on a VPSMAC instance for temporary storage of decrypted keys—the most effective way to prevent "static file leaks."
# Create a 100MB encrypted RAMDisk hdiutil create -size 100m -fs HFS+ -volname "Vault" -encryption AES-256 -attach -nomount # (Prompt: Enter password, which only exists in memory for the current session) # Mount and set permissions diskutil mount -mountPoint /Volumes/SecureData /dev/diskXsY chmod 700 /Volumes/SecureData
In your OpenClaw config, point the `secrets_path` to `/Volumes/SecureData/secrets.enc`. If the instance is rebooted or physically tampered with, the decryption keys in memory will instantly vanish, securing your data.
Phase 4: Anti-Sniffing Strategies in Isolated Environments
VPSMAC's network architecture allows users to configure independent VLANs. This means your AI agent's traffic won't cross with other tenants during automated scraping. Combined with OpenClaw v2026.2.26's **TLS Fingerprint Simulation**, you can perfectly hide your automation identity, ensuring both security and compliance.
Conclusion: Security is Your AI Agent's "Digital Armor"
Through the combination of OpenClaw v2026.2.26's Secrets auditing and VPSMAC's physically isolated Mac nodes, you have built an impenetrable "fortress" for your AI Agent. In the competitive landscape of 2026, teams that can protect their core secrets (especially keys containing user data and private model access) will be the ultimate winners.
Take Action Now: Visit the VPSMAC console, select the latest M4 Pro instance, and start your zero-leak operation journey.