Attack Resistance: Analyzing the DDoS Protection System of VPSMAC Data Centers
In the threat landscape of 2026, DDoS attacks have evolved from simple volumetric floods into surgical strikes against specific protocols like SSH, VNC, and Apple's signing services. As the world's leading M4 Mac compute platform, how does VPSMAC maintain low latency while building a Tbps-scale "Digital Great Wall"? This article dives into the underlying tech of our data center protection architecture.
Introduction: The Foundation of Reliability
For users performing automated iOS archiving, AI model training, or high-value account management, network downtime means an immediate halt in productivity. Generic cloud providers often resort to "Blackholing" traffic during large attacks, taking user services offline. At VPSMAC, we operate on a core principle: protection without disconnection.
Phase 1: Anycast Global Edge Mitigation
The first line of defense is at the edge. VPSMAC employs Anycast routing technology. When a global botnet launches an attack, traffic is automatically routed to the scrubbing node closest to the source, rather than hitting our core data centers in Hong Kong, Seoul, or Silicon Valley directly. This distributed approach neutralizes 80% of volumetric attacks before they even reach the backbone network.
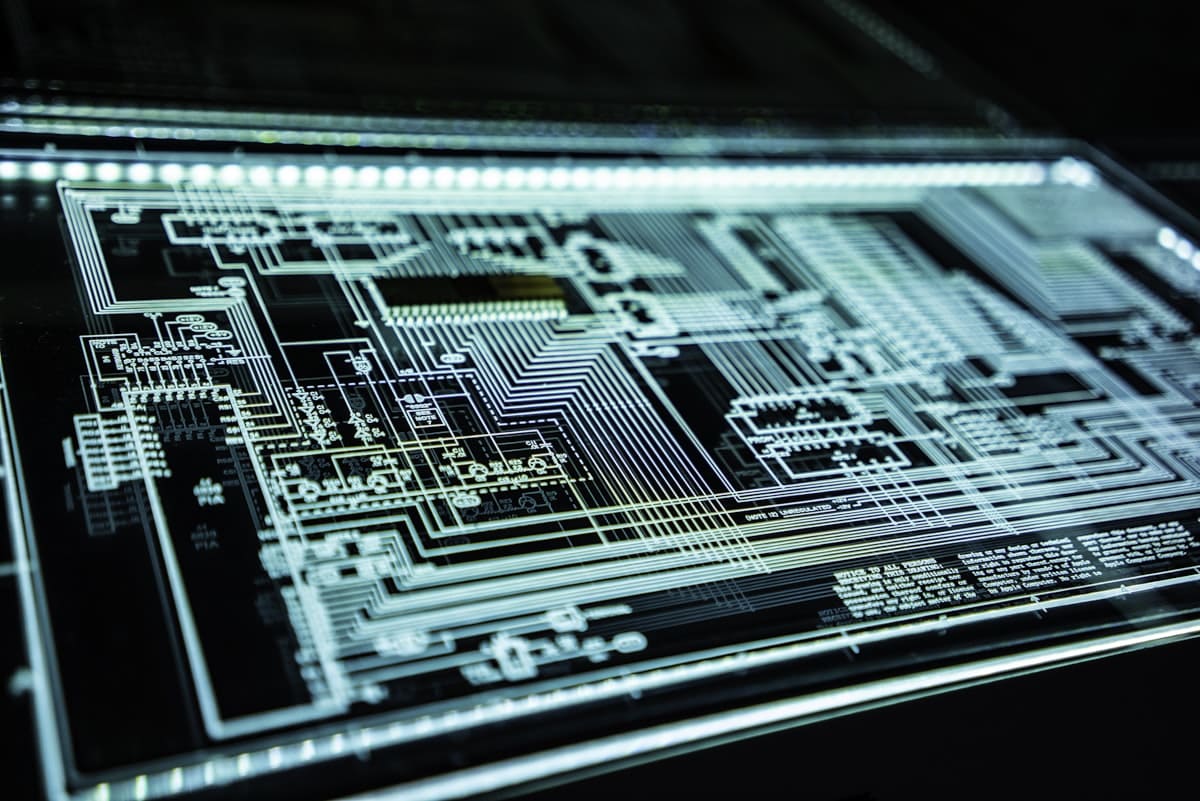
Phase 2: Tbps-Scale Hardware Scrubbing Clusters
At the entrance of our core facilities, VPSMAC deploys the latest generation of anti-DDoS hardware firewall clusters. Built on high-performance FPGA chips, these devices perform line-rate scanning of massive packet flows. Unlike traditional software filtering, our hardware clusters feature:
- Deep SYN Flood Detection: Intelligent challenges (Cookie validation) for TCP half-open attacks.
- UDP Reflection Filtering: Precise blocking of amplified traffic from NTP, DNS, and SSDP.
- ICMP Rate Limiting: Dynamic adjustment of control packet responses based on link load.
Why macOS Workloads Require Specialized Scrubbing
Remote management of macOS relies on VNC (5900) and SSH (22). These protocols are highly susceptible to "Slowloris" (slow connection) attacks or fingerprinting. VPSMAC's system includes a built-in whitelist of macOS remote protocol signatures, blocking attempts to exhaust system handles through protocol-specific vulnerabilities.
Phase 3: Layer 7 — AI-Driven Behavior Auditing
The most dangerous threats in 2026 are application-layer (L7) attacks. Attackers simulate real user behavior to overwhelm VNC rendering engines. VPSMAC has introduced an AI Traffic Behavior Audit System.
By using machine learning to analyze the frequency of clicks, scrolls, and keystrokes of legitimate users, the system can detect abnormal, high-frequency mechanized handshakes. Policies are applied within 50ms to block malicious actors, while legitimate users experience zero impact—a technology we call "Intelligent Anti-Jitter."
Phase 4: Physical Isolation — The Bare-Metal Advantage
Unlike virtualized Mac hosts using KVM or Xen, VPSMAC provides bare-metal instances. Even if other nodes in the same rack are targeted, each M4 Mac has a physically independent NIC and bus. Attack traffic cannot bleed through "side-channels" or host kernel overflows to affect your instance. Hardware-level isolation is the ultimate security bedrock.
Phase 5: BGP Intelligent Path Optimization
Beyond defense, we focus on recovery. VPSMAC is multi-homed with Tier-1 carriers like PCCW, NTT, and GTT. If one network path experiences jitter due to an attack, our intelligent BGP system automatically switches to a "clean" alternate path, ensuring your AI agents (e.g., OpenClaw) maintain low-latency connections to OpenAI/Claude nodes.
Conclusion: Security as a Service
At VPSMAC, we provide the fastest M4 Macs, but more importantly, the most secure compute environment. Tbps hardware scrubbing, AI behavior auditing, Anycast distribution, and bare-metal isolation form a quadruple shield. You can deploy your core business with confidence, leaving the infrastructure security to us and focusing entirely on development.
Experience the difference: Access the VPSMAC console, select a high-protection instance, and get finance-grade compute security.