Physical Isolation and Absolute Security: Why Finance Prefers Bare-Metal Mac Rental
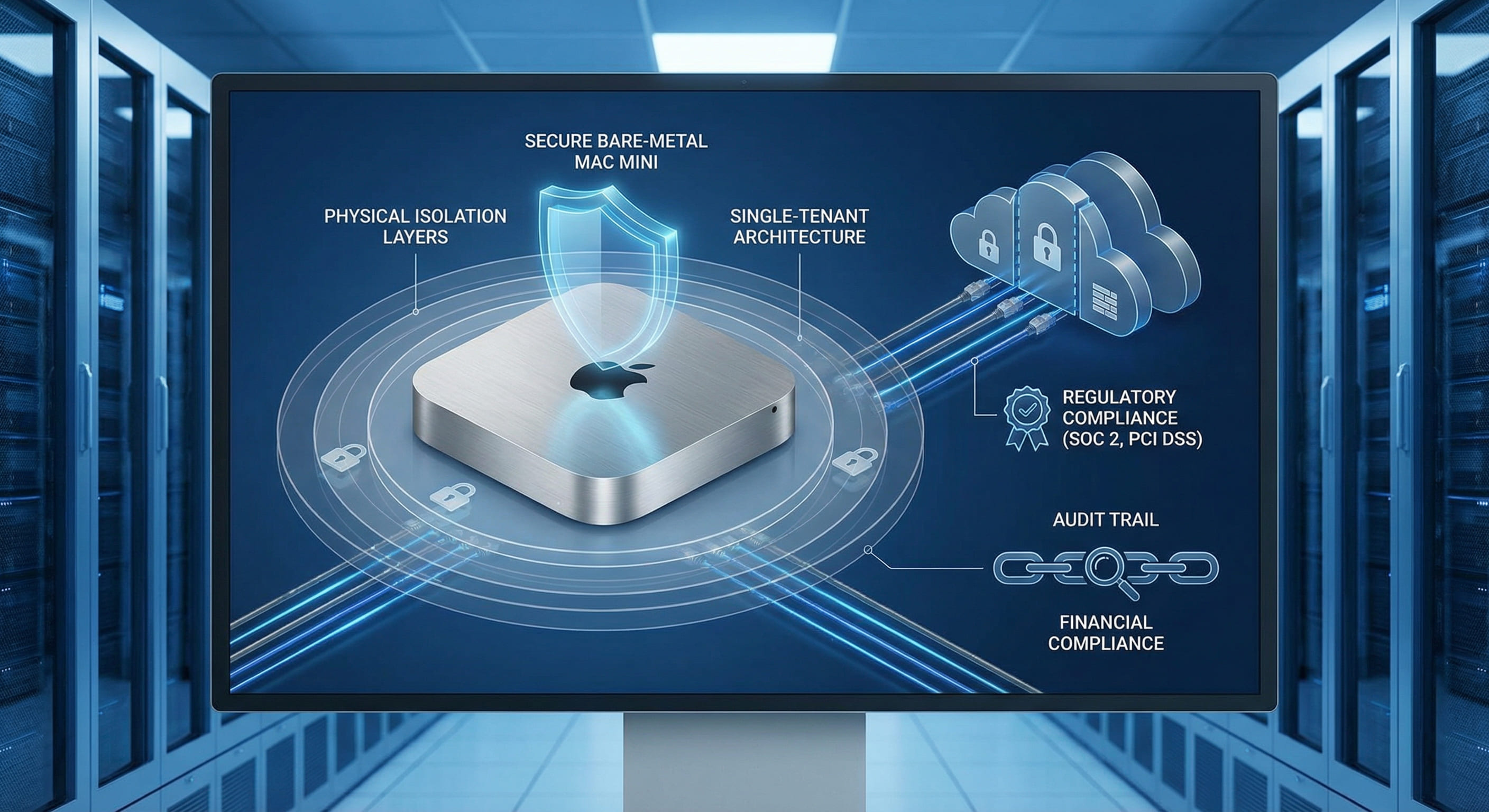
Financial institutions face some of the strictest requirements for data isolation, auditability, and regulatory compliance. This article explains why bare-metal Mac rental—single-tenant, non-virtualized Apple Silicon—has become the preferred choice for regulated macOS workloads, and how it differs from shared or virtualized cloud Mac offerings.
Why Physical Isolation Matters in Finance
Banks, asset managers, and fintech firms routinely run sensitive workloads on macOS: Xcode builds for in-house or customer-facing apps, quantitative toolchains that depend on reproducible environments, and internal automation that touches trading or compliance systems. Regulators and internal security teams increasingly demand evidence that these workloads run in physically isolated environments—no hypervisor, no co-tenancy, no shared kernel or storage with other customers. The reason is straightforward: logical isolation (VMs, containers, network segmentation) can be breached; physical isolation cannot be bypassed by a neighboring tenant because there is no neighbor.
Bare-metal rental means one physical Mac per tenant. The machine is dedicated to a single customer for the duration of the lease. No hypervisor sits between the OS and the hardware; no other customer’s processes share CPU, memory, or disk. From a compliance and audit perspective, this translates into a clear story: "This workload runs on hardware that only we use, with no multi-tenant layer in the stack." That story is much harder to tell when the same Apple Silicon is sliced into multiple VMs or when a shared cloud Mac service runs dozens of tenants on the same host.
Hypervisor vs. Bare Metal: What Auditors Care About
Virtualized Mac offerings—including public cloud Mac instances—rely on a hypervisor to partition a physical host into multiple VMs. Each VM gets its own macOS instance, but they share the same CPU, memory controllers, and often the same storage and network paths. For many development and CI use cases, that trade-off is acceptable. For financial and other highly regulated sectors, the hypervisor becomes an additional trust boundary and attack surface: firmware, host OS, and hypervisor code all sit in the chain between the guest macOS and the hardware. Auditors and security questionnaires routinely ask: "Is the environment single-tenant? Is there a hypervisor? Who has access to the host?"
With bare-metal Mac rental, the answers are simple: one tenant per machine, no hypervisor, and access is limited to the customer and the provider’s operational roles under strict procedures. There is no "host" OS that could inspect or influence the customer’s workload; the customer’s macOS runs directly on the silicon. This reduces the number of components that need to be in scope for compliance reviews and simplifies evidence collection for frameworks such as SOC 2, ISO 27001, or sector-specific rules (e.g., PCI-DSS, MiFID-related controls).
Under SOC 2 and ISO 27001, control objectives often require documentation of the logical and physical boundaries of systems that process sensitive data. A bare-metal Mac can be described as a single asset: one machine, one OS image, one tenant. The evidence package is straightforward—hardware serial, network identity, access logs, and sanitization records—without having to explain hypervisor isolation, host patching, or cross-tenant boundaries. For PCI-DSS, where segmentation and scope reduction are central, a dedicated Mac used only for build or tooling (and not cardholder data storage) can be scoped and documented with clear network and access controls; the absence of multi-tenancy removes an entire class of segmentation questions.
Data Residency and Control
Financial firms often have contractual or regulatory obligations around where data lives and who can access it. Bare-metal Mac rental can be aligned with data-residency requirements by deploying nodes in specific regions or data centers and by ensuring that only local staff and defined access controls apply. Because there is no multi-tenant storage layer, the risk of data leakage to other tenants is structurally absent; the disk in the machine is either dedicated to the customer or wiped and cryptographically sanitized before reuse. Many providers, including VPSMAC, offer clear lifecycle and sanitization policies so that customers can document how data is handled at end-of-lease.
Network isolation is another dimension. Dedicated Mac nodes can be placed in private networks, behind firewalls and VPNs, so that build artifacts, keys, and internal tools never traverse shared public endpoints. This is harder to guarantee when the same network and storage backplane are shared across many tenants in a virtualized Mac service.
Verifying Physical Isolation
Customers and auditors often want to verify that a Mac is truly bare-metal and single-tenant. On a dedicated node, the customer can run standard macOS and Unix tools to confirm the environment. For example, there is no VMware or other hypervisor device present in the hardware profile; system_profiler SPHardwareDataType and kernel extension lists reflect a native Apple Silicon Mac without virtualized devices. The machine’s serial number and model can be cross-checked with the provider’s asset records, and network topology (IP, VLAN, firewall rules) can be documented for audit. Providers such as VPSMAC supply asset identifiers and, where applicable, attestation or sanitization documentation so that security and compliance teams can close the loop: "This workload ran on this specific hardware, under these access controls, and here is what happened to the disk when the lease ended."
Performance and Predictability
Beyond compliance, bare-metal Macs deliver consistent performance. There is no noisy-neighbor effect: no other tenant can contend for CPU, GPU, or memory bandwidth. Build times and runtime behavior are reproducible, which matters for regulated workflows that must be auditable and repeatable. Benchmark data from VPSMAC and third-party comparisons show that bare-metal M4 Macs consistently match or exceed the performance of the same hardware when it is virtualized, with build and encode tasks often completing 15–25% faster and with lower variance. For finance, where build reproducibility and SLA predictability are non-negotiable, this predictability is a direct operational benefit.
In practice, a typical Xcode or CI pipeline on a shared virtualized Mac can exhibit noticeable run-to-run variance due to CPU and I/O contention. On a dedicated M4 node, the same pipeline runs with minimal variance, making it easier to set SLAs, capacity plans, and audit trails. Quantitative and research teams that depend on reproducible compute environments benefit from this consistency, as do security teams that need to re-run or validate builds in a known-good state.
Operational Model: Rent, Don’t Share
Renting a bare-metal Mac does not mean giving up operational flexibility. Customers get full SSH (and optionally VNC or similar) access to a dedicated node, can install their own toolchains and agents (e.g., OpenClaw, Jenkins, custom CI), and can treat the machine as a long-lived build or compute asset. Billing is typically by reservation period (e.g., monthly or longer), which aligns well with budget cycles and capacity planning. When a project ends or requirements change, the node can be released; the provider handles sanitization and re-provisioning. This model fits finance’s need for control and clarity: "We rent this specific machine; when we release it, here is how it is wiped and who attests to that."
Bare Metal vs. Virtualized Mac: A Quick Comparison
In a virtualized Mac setup, the provider runs a hypervisor on a physical host and allocates VMs to customers. Each VM sees a virtualized view of CPU, memory, and storage; the host OS and hypervisor manage scheduling and I/O. That design enables high density and flexible sizing but introduces shared components that auditors must consider: hypervisor code, host patching, and the possibility of side-channel or misconfiguration issues between tenants. Performance can also vary with load on the host. In a bare-metal setup, the customer gets the full machine: no hypervisor, no host OS, no co-tenancy. Audit scope is limited to the single machine and the provider’s operational procedures; performance is predictable and not affected by other customers. The trade-off is cost and flexibility: bare metal is typically priced per machine and does not offer sub-machine sizing, but for regulated and performance-sensitive workloads, the clarity and control are often worth it.
When Bare Metal Is the Right Fit
Bare-metal Mac rental is not the only option for every team. It is most compelling when (1) compliance or security policy explicitly or implicitly requires single-tenant, non-virtualized infrastructure; (2) workloads are sensitive enough that the absence of a hypervisor and co-tenancy is a meaningful risk reduction; (3) performance and predictability matter for SLAs or auditability; or (4) data-residency and data-control requirements are easier to satisfy with a dedicated machine and clear lifecycle. Financial institutions, healthcare-adjacent apps, and enterprises with strict internal security standards are typical adopters.
Concrete scenarios include: a bank’s internal iOS app team building and signing releases on a Mac that must be documented for internal audit; a quant shop running reproducible research toolchains on macOS with no shared infrastructure; a fintech firm that must prove to partners or regulators that build and test environments are physically isolated. In each case, the ability to say "this workload runs on a machine that only we use, with no hypervisor and no co-tenant" simplifies questionnaires and audit evidence.
For teams that only need occasional Mac access for light builds or demos, a shared or virtualized Mac service may be sufficient. But when the use case involves regulated data, reproducible builds, or long-running automation that must be explainable to auditors, the physical isolation of a bare-metal Mac rental is a strong fit.
Summary
Physical isolation—one physical Mac per tenant, no hypervisor, no co-tenancy—provides the highest assurance level for macOS workloads in regulated industries. Finance and other sectors with strict compliance requirements increasingly prefer bare-metal Mac rental because it simplifies audit narratives, reduces attack surface, supports data-residency and control requirements, and delivers predictable performance. VPSMAC provides dedicated M4 Mac nodes on a bare-metal basis, with clear lifecycle and access controls, so that teams can run sensitive macOS workloads in an infrastructure model that matches both technical and regulatory expectations.